The pentesterthat runs itself.
Offensive security that finds real exploits on your schedule, every deploy, and as your attack surface evolves.
Trusted by security teams across Fintech, SaaS & Education, Enterprise & Telecom, Security & Critical Infrastructure

The 51-week gap
Your Q1 pentest doesn't cover what you shipped in Q3.
One sprint later, your attack surface has moved. One quarter later, the test is a fossil. Every new deploy, API, and identity change happens between tests and lands in production untested.
Your engineering team ships features, APIs, and identity changes every week of the year.
One scheduled engagement. Scoped months ahead, delivered weeks later, captures a snapshot that ages from day one.
Every change between tests lands in production without an exploit-grade review.
What we ship
Here's what we prove.
SecureLayer7 finds what others miss. Proven by CVSS 9.4-9.9 zero-days. Shipped through three products: an AI pentest agent, an on-prem API scanner, and a platform that replaces the PDF.
Start where you are.
Three doors. Same depth behind each.
Scope a pentest
Red Team, Cloud, Source Code, IoT, or a custom surface, delivered by the same team behind our CVE disclosures.
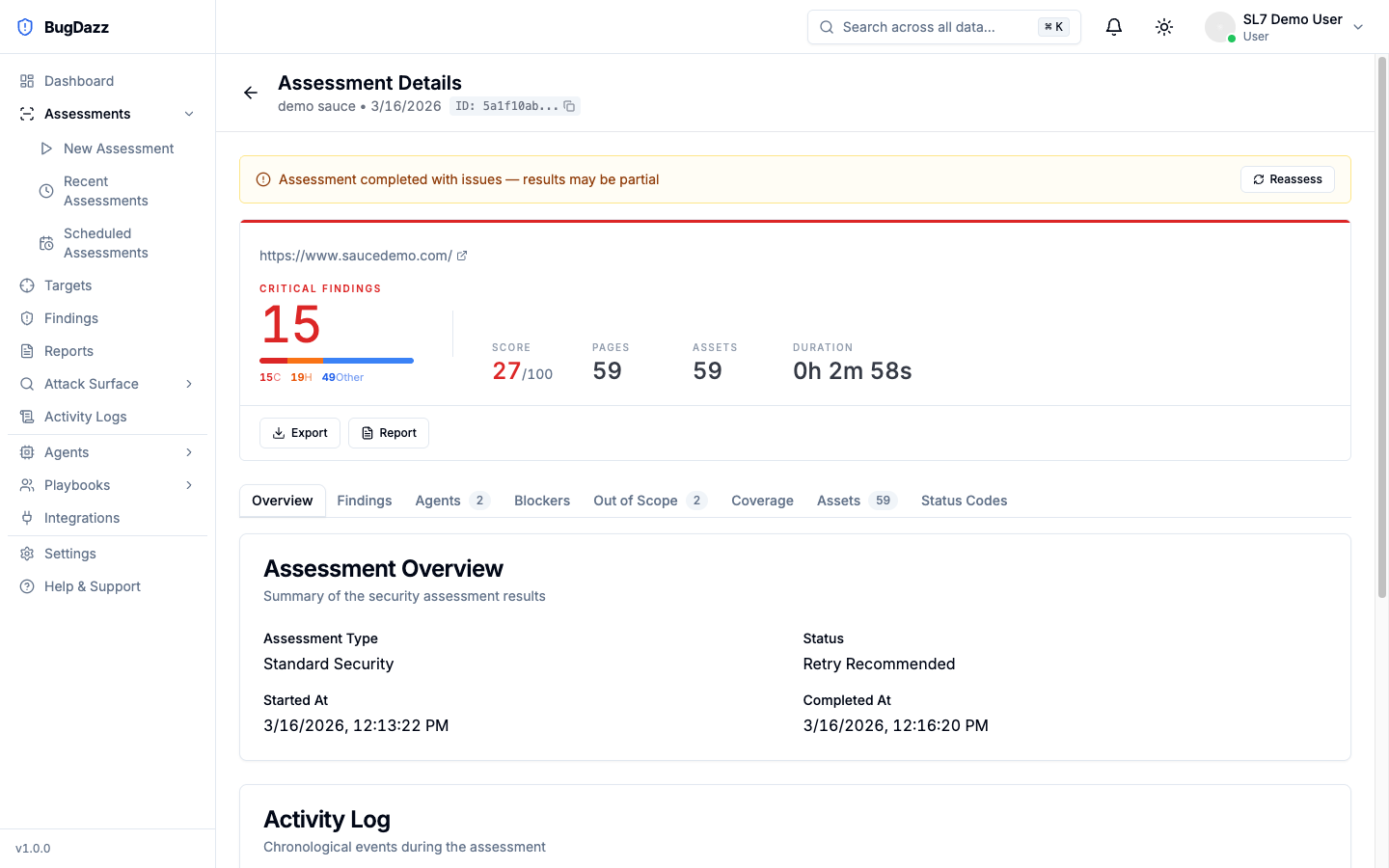
See Autonomous
AI agents that attack Web, API, and Active Directory on the schedule you set. Findings in JIRA, Slack, and CI/CD the moment they are proven.
Offensive doctrine
Find. Probe. Exploit.
SecureLayer7's offensive methodology. Refined over 14 years of research, reviewed on Gartner Peer Insights, validated every day by the security teams using it.
Aligned to the CTEM framework
Find
Continuous EASM. New web assets, APIs, cloud resources, identity providers, and shadow infrastructure the CMDB doesn't know about. The Discovery phase of your CTEM program, always on.
Probe
Custom test cases built per asset, not a canned CVE checklist. Business-logic flaws, authentication gaps, chained conditions, and the weak paths that only show up under pressure.
Exploit
Every finding exploited, not flagged. Proof of compromise, evidence trail, short video of the attack, fix path, re-test included. The Validation phase of your CTEM program, in a form auditors and insurers accept.
Research ledger
Recent SL7 Lab disclosures.
Coordinated-disclosure advisories published by SecureLayer7 research.
On record
Why SecureLayer7?
14 years of offensive research. Every claim backed by a live CVE or a proven exploit.



Mapped to engagement requirements across
SOC 2 Type IIPCI DSSHIPAAISO/IEC 27001GDPRNIST CSFand others
High-risk vulnerabilities
Exploitable findings proven across customer fleets, most inside systems that had already passed previous audits.
Engagements completed
Web apps, APIs, mobile, cloud, AI systems, internal networks. Across fintech, SaaS, healthtech, and enterprise.
See Research & DisclosuresLatest CVSS zero-day
n8n full system compromise, disclosed by SL7 Lab. Part of an ongoing CVE research track record in production systems.
Recognized by



In production since 2012
Fourteen years, in the open.
Specific, dated, verifiable. Conference talks, named CVE credits, customer endorsements. The receipts are on the press page.
- 40+CVE disclosures
- 24Press mentions
- 6International stages
Hear from our clients
“Thank you for being our pentest partners. Our user base is safer because of y'all.”
Vinay Hiremath
Co-founder, Loom
Research & insights