Application security testing
Find every security issue before it ships.
Whatever your stack ships, Web, Mobile, Thick Client, API (REST · GraphQL · gRPC · MQTT), Cloud. Tested manually by operators who publish CVEs. Every finding lands with a working proof-of-exploit, developer-ready fix guidance, and a re-test.
Coverage
Web · Mobile · Thick Client · API · Cloud, every application class.
Evidence
Working proof-of-exploit and developer-ready fix guidance on every finding.
Re-test included
We verify your fixes at no extra cost. One engagement, closed loop.
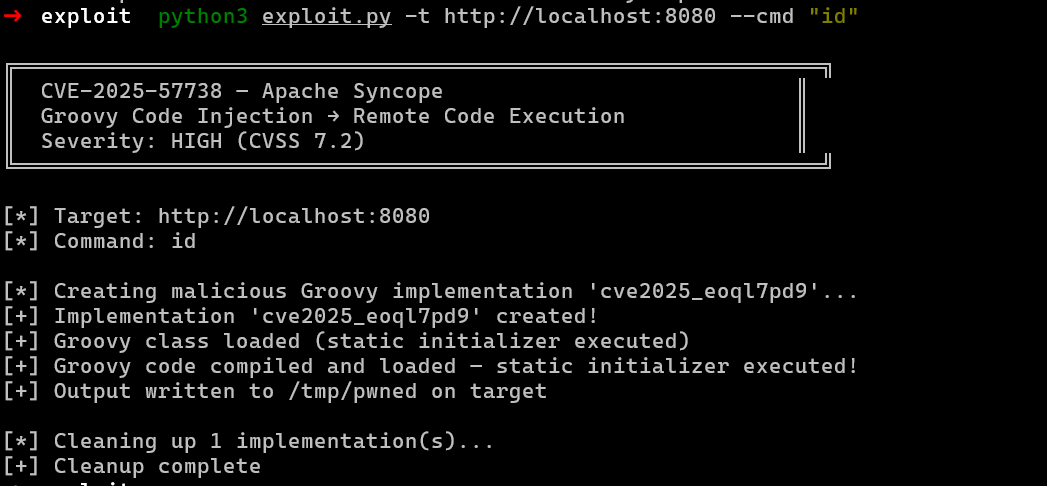
A single dependency typosquat ships RCE before your next sprint review.
Trusted by security teams across Fintech, SaaS & Education, Enterprise & Telecom, Security & Critical Infrastructure

On record
Why application security testing
Risk lives in your application's logic.
Real risk lives in your auth model, your workflow logic, your API resolvers. AppSec testing reads the application like an attacker reads it, from the outside, with intent, until small flaws compound into something the dev team can ship a fix for and the auditor will accept.

What we pentest
Every application we ship against.
Pick the application class, same depth across each. Manual chained-exploit testing on every surface, not a scanner sweep.
Web Application
Server-rendered and SPA web apps. Auth flows, session handling, OAuth/OIDC, multi-tenant boundaries, business logic, security headers, SSRF, chained against your real user roles.
PAST THE SAMPLE REPORT.
What 47 chained pre-auth exploits actually look like.
- 01IDOR to admin
Object-reference flaws plus weak session validation. Anonymous to admin.
- 02Mass assignment to RCE
Body-bound model fields overwrite admin properties, escalate into deserialization.
- 03SSRF to cloud role
Server-side request forgery into IMDS for AWS role assumption from anonymous endpoints.
- 04OAuth to account takeover
State-parameter prediction, PKCE downgrade, redirect-URI bypass.
- 05Business logic to privilege
Time-of-check race against payment, account merge, role assignment.
What we test —
Eight application surfaces. One engagement.
These are the surfaces SecureLayer7's app-sec practice operates across. Every surface in scope by default; intensity tunes per engagement.
Authentication & Session
Login bypass, session fixation, token prediction, password reset flaws, MFA weaknesses, federation bypass, OAuth/OIDC misconfig.
Authorization & Access Control
IDOR, broken object-level auth, privilege escalation, multi-tenant bleed, role/scope-checking gaps in API + UI.
Business Logic
Price manipulation, workflow abuse, state-machine bypass, race conditions — the chained exploits unique to your application.
API surfaces (REST · GraphQL · gRPC · MQTT)
REST + GraphQL — BOLA, mass assignment, query-cost, schema introspection. gRPC — protobuf field abuse, reflection leaks, streaming-method DoS, mTLS misconfig. MQTT — broker auth, ACL bypass, retained-message exposure, topic-injection across IoT/real-time brokers.
Data Storage & Encryption
Local storage exposure, key management, encryption-at-rest verification, transit ciphers, certificate pinning.
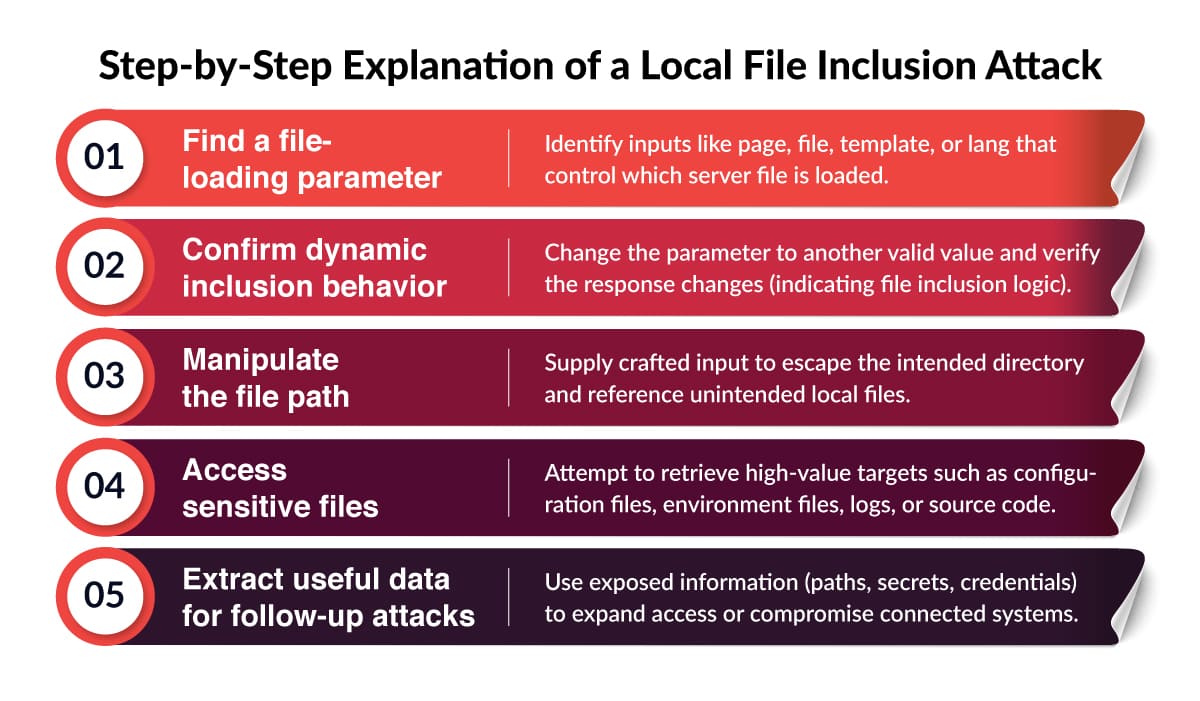
Injection & Execution
SQLi, XXE, SSTI, command injection, deserialization, prototype pollution — tested manually with chained exploits, not just signatures.
Configuration & Secrets
Exposed admin panels, misconfigured headers, leaked secrets in JS bundles, third-party SDK exposure, server-side config drift.
Web3 / Smart Contracts
Solidity audit (reentrancy, integer over/underflow, access-control gaps, unchecked external calls, gas-griefing, oracle manipulation), EIP-712 signature reuse, wallet-connect phishing flows, multicall + delegatecall abuse, ERC-20/ERC-721 approve-and-drain, bridge replay, MEV / front-running on dApp UX.
Findings inside systems that already passed audit. The chain runs through gaps no checklist names.
“Compliance is a snapshot. Application pentest is the stress test the snapshot can't show, the chain an attacker actually walks when your auditor isn't watching.”
APPLICATION SECURITY METHODOLOGY.
Eight phases. Logic to dependency.
Threat-modeled to your application's user roles, data flows, and business logic. Not a template we run against every engagement.
- 01Recon & enumeration
- 02Scope & threat-model
- 03Static analysis
- 04Active testing
- 05App & API analysis
- 06Vulnerability analysis
- 07Remediation guidance
- 08Patch verification
Pentester credentials
Proven expertise in application security.
Pentesters across the SecureLayer7 practice carry the certifications buyers ask procurement to verify.
Insights
Application security Resources.
AppSec reviewer notes: chained authn/authz bugs, business-logic findings, and the CVE write-ups we publish after disclosures.
Meet our expert
One lead across every app you ship.
Nivedita Singh
Security Advisor & Engagement Lead
10+
Years in application security
300+
Engagements led
99.7%
On-time delivery rate
Nivedita scopes application-security engagements against your architecture and risk priorities, then guides the pod from kick-off through final report and re-test.
- Scopes web, API, mobile, and SaaS-tenant engagements against your real risk model.
- Owns kick-off, mid-engagement check-ins, and live walkthrough of every finding.
- Drives remediation review and re-test until every finding is closed.

Ready to scope an application pentest? Book 30 minutes with Nivedita to walk through your stack, scope, and timeline.
Common procurement questions
What buyers ask about application security testing.
Six questions procurement teams ask before signing an AppSec SOW. Answered against our methodology and your auditor.
Show all 6 questionsShow less
Have a procurement question not listed here?
For startups
Pre-Series A? Apply for the startup program.
A single Autonomous app pentest, CREST-aligned report, engagement-lead signoff, retest included, heavily discounted for pre-Series A startups passing enterprise procurement or SOC 2 due diligence. Eligibility verified on application.
Tested by industry.
The bug classes named below come from real engagements in each sector. Pick the closest fit.
Tech SaaS
Multi-tenant SaaS, customer-facing portals, admin consoles tested end-to-end.

Sample engagement report
See what arrives in your inbox.
A pre-vetted sample report: full vulnerability narrative, working PoC, code-level fix guidance. Sent on request after a 5-minute scoping call.