Mobile app penetration testing
Mobile Application Penetration Testing Two stores, two binaries, one method.
Mobile application penetration testing across iOS · Android, tested by hand for insecure deeplink hijack, Keychain / Keystore mishandling, addJavascriptInterface RCE, intent injection, TLS-pinning bypass, and binary-extracted secrets. Every finding lands with a working proof-of-exploit, the patch path, and a verified re-test.
iOS · Android
Native, hybrid, and cross-platform builds, read by hand, hooked at runtime.
Static + Dynamic
IPA / APK reviewed and the binary instrumented under Frida, Objection, and a real device proxy.
Re-test included
We verify your fixes at no extra cost. One engagement, closed loop.
Reverse-engineering your binary takes a researcher one evening, and your secrets ship inside it.
Trusted by security teams across Fintech, SaaS & Education, Enterprise & Telecom, Security & Critical Infrastructure

On record
Why mobile pentest needs runtime
Static stops at the surface. Runtime tells the truth.
MAST scanners read what the binary admits to: manifest exports, declared permissions, declared TLS posture. None of that survives contact with a real device under instrumentation. Frida hooks the live process. Objection bypasses pin checks. A proxy reads the network as the app sees it. Only at runtime do you see the secrets that resolve from the Keychain, the deeplink that sidesteps auth, the WebView bridge that hands JS the file system, the API call the app makes when it thinks no one is watching. We deliver the chain in motion: source, binary, hook, exploit, the patch path, the re-test.

MOBILE PENTESTS DELIVERED.
Two stores. Counted, not claimed.
Native binaries, hybrid frameworks, and the backends they call. Each reviewed by hand and hooked at runtime. Numbers below are engagements SecureLayer7 has actually closed, not market-size estimates.
Manual review of DEX, Smali, Kotlin, and Java. Frida runtime hooks, Keystore mishandling, intent injection across exported components.
Manual review of Mach-O, Swift, and Objective-C. Keychain access-control flaws, ATS bypass, Universal Links auth gaps under a live-device proxy.
iOS and Android run side-by-side under one scope. The shared mobile backend is included by default. One engagement, two binaries, one report.
TWO STORES.
The runtime classes both iOS and Android share, plus the platform-specific ones.
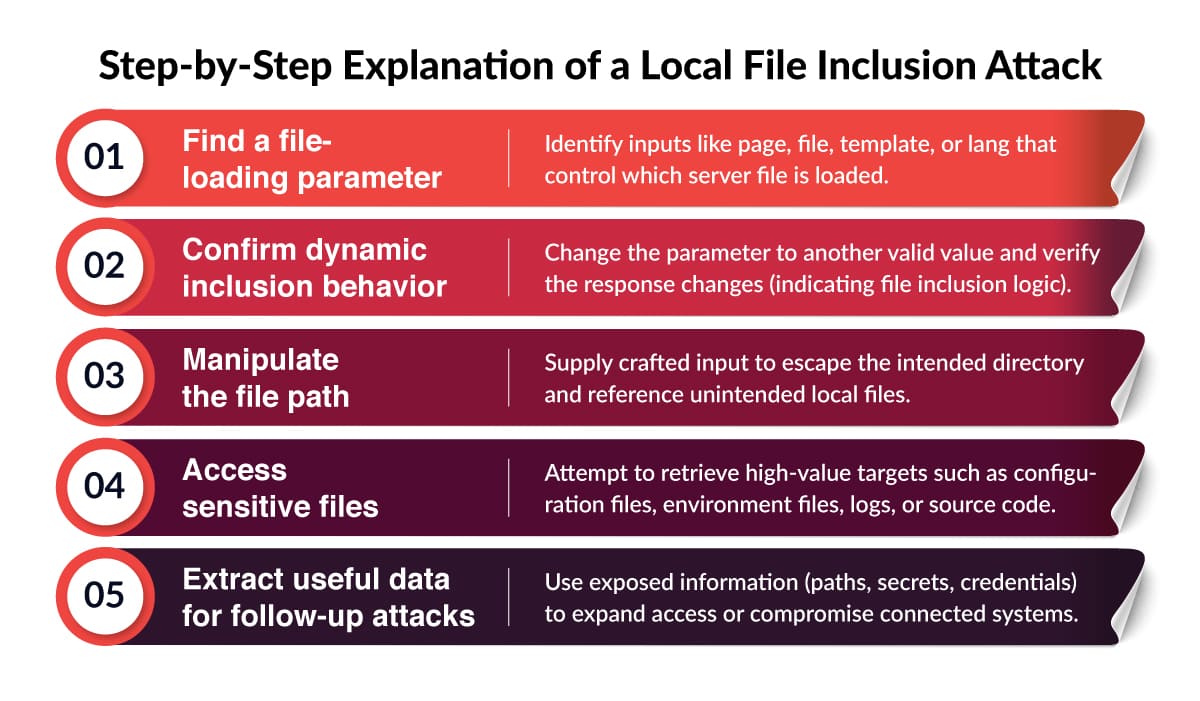
- 01Frida runtime hooks
We attach Frida or Objection to bypass client-side controls and read live state from running iOS and Android processes.
- 02Keychain and Keystore drift
iOS Keychain ACL misconfig (kSecAttrAccessibleAlways) and Android Keystore unbound keys that survive lock-screen prompts.
- 03Deep-link account hijack
Custom-scheme and Universal Link collisions abused to land the attacker inside an authenticated session without a tap.
- 04Intent redirection
Exported Android activities and pending-intent reuse turned into cross-app privilege escalation and forced token exfiltration.
- 05WebView and JS bridge
addJavascriptInterface RCE, file:// XSS, and bridge methods that hand the WebView keys to the native shell.
- 06Pinning and biometric bypass
TLS pinning unhooked at SSLSocketFactory or NSURLSession, plus LAContext callbacks faked to skip Face ID and BiometricPrompt.
- 07Binary-extracted secrets
Strings, .plist, Smali, and DEX inspection that lifts API keys, signing certs, and back-end URLs straight out of the shipped artifact.
What we cover —
Eight layers. Every one read by hand and hooked at runtime.
Mobile is a stack: the binary, the runtime, the IPC, the network, the backend it actually calls. We test each layer in the language and toolchain your team ships in.
iOS native — Swift · Objective-C · SwiftUI
Keychain access-control mishandling, ATS bypass via NSAllowsArbitraryLoads, URL-scheme hijack, Universal Links validation gaps, App Group leakage, jailbreak-detection bypass under Frida.
Android native — Kotlin · Java · Compose
Exported-activity hijack, intent injection, ContentProvider authority abuse, insecure SharedPreferences, Keystore mishandling, root-detection bypass, Smali patch under MOBSF / objection.
Hybrid — React Native · Flutter · Cordova · Ionic
JS-bridge exposure, deserialised props from native to JS, asset bundle tampering, hot-reload server abuse on dev builds shipped to prod, Flutter snapshot reverse-engineering.
WebView surface
addJavascriptInterface RCE, file:// URI access from a remote origin, mixed content, intent:// scheme abuse, JS-to-native bridge auth gaps, cookie scope leakage between WebView and host app.
Inter-process communication (IPC)
Android intents, iOS URL schemes, Universal Links, App Links, broadcast receivers, deep-link OAuth-state mishandling, activity-stack tampering, share-sheet payload injection.
Mobile API & backend
REST and GraphQL endpoints called only by the mobile client — broken object-level authZ, mass assignment, mobile-only auth flows, refresh-token rotation gaps, abuse of mobile-specific headers as trust signals.
Embedded SDKs & native libs
Third-party SDKs (analytics, payments, in-app messaging) audited for over-permission and data exfiltration. JNI / NDK native libs reviewed for buffer overflow, format-string, use-after-free, and unsafe FFI boundaries.
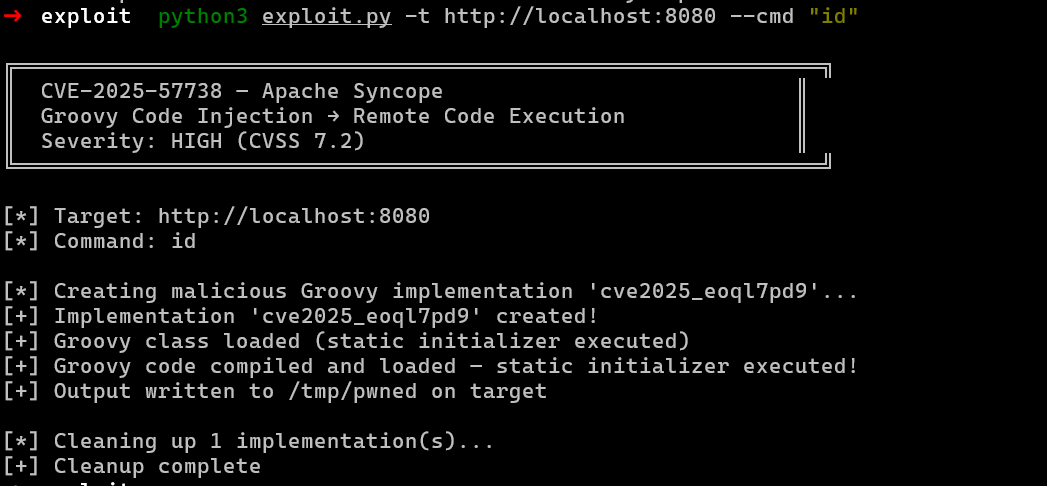
Reverse engineering & resilience
Mach-O / DEX / Smali disassembly under IDA, Ghidra, jadx. Hardcoded API keys, signing material, and crypto secrets extracted from the binary. Control-flow obfuscation and tamper-detection tested against real bypasses, not vendor claims.
MOBILE METHODOLOGY.
Eight phases. Binary to backend.
Threat-modelled to your platform mix, build pipeline, and backend reach. Not a checklist run against every IPA we receive.
- 01Scope & threat-model
- 02Source & binary recon
- 03Static analysis
- 04Dynamic instrumentation
- 05Network & backend
- 06Reverse engineering
- 07Exploit synthesis
- 08Patch verification
Insights
Mobile security Resources.
Mobile reviewer write-ups: cert-pinning bypass, deep-link auth bugs, and the Android/iOS findings our pentesters file at scale.
Meet our engagement lead
Meet our engagement lead
John Dill
vCISO at SecureLayer7
5,000+
Mobile pentests scoped
iOS · Android
Platforms in scope
98%
Engagement-lead close rate
John scopes mobile pentest engagements against your platform mix, build pipeline, and backend reach. He runs kick-off, status reviews, and sign-off so the mobile pod stays heads-down on the binary.
- Scopes engagements across iOS, Android, hybrid (RN, Flutter), and mobile-API surfaces against your real risk model.
- Owns kick-off, mid-engagement walkthroughs, and live review of every finding.
- Drives remediation review and re-test until every finding is closed and proven.
Ready to scope a mobile pentest? Book 30 minutes with John to walk through your iOS and Android builds, hybrid stack, and timeline.
Book a 30-min callWhitepaper
Mobile-app control bypass.
Original research on bypassing Appdome mobile-app privacy and security controls. Read before you assume RASP / shielding fully protects a release.
Common procurement questions
What buyers ask about mobile application pentesting.
Six questions procurement teams send before signing a mobile pentest SOW. Answered against our methodology and your auditor.
Show all 6 questionsShow less
Have a procurement question not listed here?
Tested by industry.
The bug classes named below come from real engagements in each sector. Pick the closest fit.
HealthTech
Patient apps, telehealth clients, PHI capture, prescription pickup flows.

Sample engagement report
See what arrives in your inbox.
A pre-vetted sample report: full mobile-pentest narrative, working PoC on a real device, the patch path, and the re-test confirmation. Sent on request after a 5-minute scoping call.