CREST
Accredited company & testers
SecureLayer7 testers abuse Kubernetes the way a motivated actor does after they already have a foothold: reachable kubelets, RBAC verbs that chain to cluster-admin, admission stacks that look fine on paper, and tokens that survive longer than the pod. You get ranked chains with manifests, kubectl transcripts, fixes written for platform engineers, and a re-test so audit sees proof, not debate.
Manual cluster testing · CVE-disclosing researchers · Audit-ready kill-chain reporting

We start from workloads and identities your threat model already treats as risky, then move toward control plane and supply-chain edges. Not a perimeter-only review.
Manifests, commands, and remediation your engineers can drop straight into tickets. Not a passing CIS row that still leaves cluster-admin within reach.
After you ship patches, we re-run the chain. Written confirmation for each closed pivot, at no extra fee.
One pod escape and the entire control plane is one kubectl call away.
Trusted by security teams across Fintech, SaaS & Education, Enterprise & Telecom, Security & Critical Infrastructure

On record



Why benchmarks greenwash risk
kube-bench, Trivy, and CIS profiles grade configuration snapshots. They rarely prove chained impact: compromised workload, abused kubelet API, lateral hops across namespaces, cluster-admin. We string those steps the way an adversary would, so platform leads and auditors get a narrative they can follow without guessing.

IN SCOPE.
Cluster-role bindings, escalation verbs, impersonation, token-creator paths to cluster-admin.
Privileged pods, hostPath mounts, capabilities, securityContext drift, runtime breakout.
NetworkPolicy gaps, service mesh trust, ingress to internal services, DNS rebinding inside-cluster.
Registry trust, admission controllers, mutating webhooks, sidecar injection, signed-image bypass.
POD-ESCAPE PATHS.
Where a misconfigured cluster gives an attacker root on the host.
Pod mounts / from the host, attacker writes to /etc/kubernetes/manifests, static-pod becomes a privileged kubelet workload.
securityContext.privileged true, capabilities SYS_ADMIN, mount cgroups release_agent, execute on the node as root.
Auto-mounted token in a compromised pod, kubectl auth can-i wildcard, list secrets across every namespace.
Developer kubeconfig left in a CI runner image, cluster-admin context survives image rebuild, attacker reuses it from outside.
etcd endpoint exposed on the control-plane subnet without client-cert auth, dump every Secret object in plaintext.
ValidatingAdmissionWebhook fail-open on timeout, attacker submits a Pod that the policy would have blocked.
Internal service trusts the ingress identity, attacker who reaches the service mesh from a sidecar replays cluster-internal calls.
on record ,
CREST is the standard for offensive security execution. CERT-In, SOC 2 Type II, and ISO/IEC 27001 cover how SecureLayer7 handles your cluster evidence, Kubernetes artefacts, and your engagement record.
Accredited company & testers
Empanelled auditor
Independently audited
Information Security Management
Mapped to audit requirements across
Scope ,
Most cluster reviews stop at isolated findings. We chain control plane exposure, workload breakout, identity and secrets, and supply-chain trust in one engagement, mapped to your topology and exercised manually against the bug classes that appear once an attacker already has a foothold.
kube-apiserver anonymous-auth, etcd 2379 exposure, kubelet 10250 unauth, scheduler / controller-manager metrics leak, admission-webhook race, audit-policy gap, /healthz info disclosure, in-cluster API server SSRF.
Privileged-container escape, hostPath / hostNetwork / hostPID abuse, SYS_ADMIN & NET_RAW capability misuse, missing seccomp / AppArmor, PodSecurityStandards bypass, NetworkPolicy default-allow, sidecar trust-boundary leak, ConfigMap secrets leak.
ServiceAccount token theft and replay, escalate / impersonate / bind verb chaining, over-scoped ClusterRoleBinding, projected-token reuse across namespaces, IRSA / Workload-Identity confusion, External-Secrets misconfig, kubectl auth can-i blind spots.
Mutating-webhook abuse, unsigned-image admission, ImagePullSecret leak, base-image typosquat, SBOM tampering, GitOps repo and pipeline takeover, Helm-chart values injection, registry-credential reuse across clusters.
KUBERNETES METHODOLOGY.
Scoped to your topology, namespaces, RBAC graph, admission controllers, and how images actually ship. We stress APIs, controllers, workloads, and pipelines until impact is demonstrated or ruled out. Deliverables include prerequisites, blast radius, and remediation sized for how your platform team ships change.
Insights
Notes from operators who publish CVE research and ship fixes in the open: Kubernetes hardening, exploit chains, and lessons from real cluster engagements.
Meet our engagement lead
vCISO at SecureLayer7
15+
Years in offensive security
150+
Engagements led to date
99.99%
On-time engagement delivery
John owns Kubernetes engagements from scope to re-test. Topology and RBAC graph become the test plan your platform org recognises. He stays through live walkthroughs, remediation, and re-test.
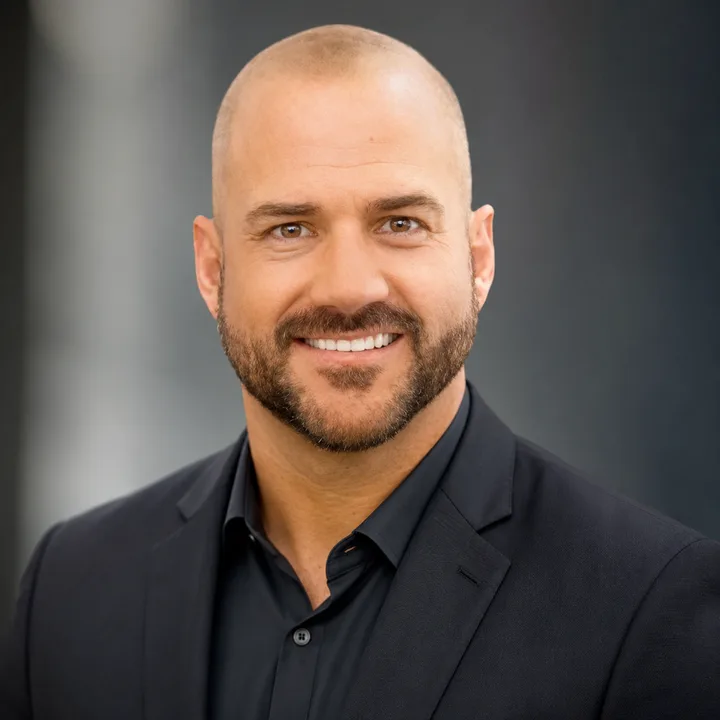
When your next board or audit cycle asks how far someone moves from one bad pod, book 30 minutes with John. Topology, RBAC graph, and timeline on one call.
Book a 30-min callCommon procurement questions
Six questions platform and security teams send before signing a Kubernetes pentest SOW, pricing, duration, scope, cloud coverage, and how the engagement differs from kube-bench or CIS audits.
Have a procurement question not listed here?
The bug classes named below come from real engagements in each sector. Pick the closest fit.
Banking workloads on k8s, secret-rotation, PCI segmentation in service mesh.
HIPAA-aligned k8s workloads, PHI-handling pods, audit-log retention paths.

Sample engagement report
The sample pack walks YAML-shaped edges, RBAC escalation, and the shortest path from workload compromise to cluster-wide impact. Redacted from real engagements, formatted for risk and audit readers. Sent after a short scoping call so examples match your environment.